Conquer supports a wide range of IT support services tailored to meet your goals and support your tools, applications, and infrastructure.
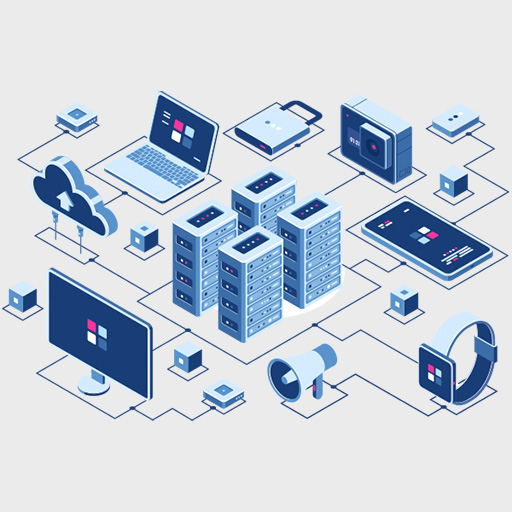
IT Infrastructure Management
- Network Infrastructure Management - Stretching secure infrastructure solutions across the integrated network ecosystem, racing from design, implementation, and maintenance.
- Server Infrastructure Management – A holistic, solid server infrastructure plan with regular evaluations and monitoring helps your business move forward in the digital economy.
- Storage Infrastructure Management – Transform your infrastructure by enabling automated, integrated storage virtualization across multiple operating systems to reduce costs and improve efficiency.
- Cloud Infrastructure Management – Set your business up with on-premises cloud infrastructure management to deliver an exceptional digital experience with better flexibility and customization.
IT Support Services
- Help Desk and Technical Support – In-house IT help desk provides innovative solutions to every problem that affects productivity through automated resolution processes.
- Remote Desktop Support - Comprehensive remote support solutions on key systems enable businesses to operate in challenging circumstances, knowing their team will be supported at every location.
- Onsite Support Services – Overcome the challenges of telework and networking and fill the tech gap with the best onsite support services to reach regions from domestic to overseas geographical boundaries.
- Hardware and Software Support – Discover the right equipment to meet your needs and budget to ensure smooth and cost-effective business operations.


IT Security Management
- Security Assessment and Auditing - Enhance the visibility of your growing network with the right assessment practices and auditing tools to automate the discovery of potential hard-to-find issues and get the power to resolve them with improved security.
- IT Security Consulting Services – Protect your business's digital assets, data, and users from cyber threats by accessing the powerful ability of consulting services integrated into a single platform for maximum productivity.
Cloud Services Management
Conquer’s broader mission is to manage hybrid environments and resources while managing, optimizing, and enhancing their cloud efficiently.
- Cloud Infrastructure Management – Supported by the round-the-clock team and efficient network infrastructure to monitor, scan, update patches, integrate, and connect the network with core business objectives.
- Cloud Hosting and Managed Services – Explore and extend new avenues for your business to maximize efficiency, manage risk and enhance your growth across borders with multi-layered, managed virtual safety.
- Cloud Security Management – Get assured of data security and early access across every cloud service and application of your organization, gaining you better control on every service level while you achieve business continuity.


IT Consulting Services
- IT Strategy and Planning – Build a vision of the initiatives required to light your IT ability with your core business goals with a clear understanding of the timeframe, estimated cost, and sequence
- Digital Transformation Consulting – Develop and execute a distinct and strategic technology roadmap for digital transformation associated with your business goals.
- IT Project Management – Enriched with necessary resources and technology facilities to support your organization in executing projects successfully, with a guaranteed high return on your initial investment.
- Cybersecurity Consulting – Get the confidence to lead the transformation and adapt to the latest technology without compromising your cybersecurity by implementing rigorous measures in the right direction.



